How Sovereign Clouds are Redefining Digital Privacy
From government agencies to healthcare providers, organizations are discovering that true digital sovereignty means owning the entire stack—not renting it from AWS.
Metadata:
🟡 Level: Intermediate
⏱️ Reading Time: minutes
🏷️ Topic: Cloud Infrastructure, Virtualization, Data Sovereignty

1. Introduction: The Return of Control
You built your career mastering Linux servers. Then the cloud arrived, and suddenly “infrastructure” meant trusting hyperscalers with your data, workloads, and control plane. For years, it made sense—scalability, managed services, global reach.
But the tide is turning. Governments are repatriating systems. Enterprises are questioning vendor lock-in. And Linux admins are realizing they never needed to surrender control in the first place.
This is the sovereign cloud movement: modern infrastructure with Kubernetes, software-defined networking, and API-driven automation—but you own the stack, not AWS. It’s not about going backwards; it’s about moving forward with accountability.
For many Linux administrators, transitioning to the public cloud was a pragmatic choice driven by workload demands rather than ideology.

However, large organizations and governments are increasingly moving critical systems from global hyperscalers to sovereign clouds—environments under local jurisdiction, built on open platforms, and operated by trusted teams. This transition isn’t about rejecting cloud innovations but about reclaiming ownership over the control plane.
2. Why Sovereign Clouds Are Gaining Momentum
The shift to sovereign clouds isn’t ideological—it’s practical. Several converging factors are driving organizations back to self-hosted infrastructure:
Regulatory Reality
GDPR, data residency laws, and sector-specific compliance requirements make hyperscaler clouds legally risky. A single AWS region doesn’t guarantee data sovereignty when the vendor operates under U.S. jurisdiction and may be subject to foreign government access requests.
Cost Control
Hyperscaler billing is unpredictable. Egress fees, premium support contracts, and vendor lock-in pricing models add up quickly. With sovereign clouds, capital expenditure is predictable—you know exactly what your infrastructure costs, with no surprise bills at month’s end.
Cost Control
Hyperscaler billing is unpredictable. Egress fees, premium support contracts, and vendor lock-in pricing models add up quickly. With sovereign clouds, capital expenditure is predictable—you know exactly what your infrastructure costs, with no surprise bills at month’s end.
Operational Transparency
In a hyperscaler environment, you don’t know what’s running underneath your workloads. Shared infrastructure, proprietary hypervisors, and opaque incident response processes mean you’re operating in someone else’s black box. With sovereign infrastructure, you control every layer—from BIOS configuration to application deployment.
Vendor Independence
Relying on a single hyperscaler’s roadmap means you’re at their mercy for features, pricing, and service availability. Sovereign clouds built on open platforms (Proxmox VE, OpenStack, Kubernetes) give you the flexibility to adapt without vendor constraints or the risk of services being deprecated beneath you.
Cost Control
Hyperscaler billing is unpredictable. Egress fees, premium support contracts, and vendor lock-in pricing models add up quickly. With sovereign clouds, capital expenditure is predictable—you know exactly what your infrastructure costs, with no surprise bills at month’s end.
To expand this section for your article, we need to move beyond simple definitions and dive into the “Why” and “How” from a Sovereign Cloud perspective. The goal is to show how these platforms actually give power back to the admin by removing the proprietary “black box” found in hyperscalers.
Here is an expanded version of Section 3, structured for clarity and depth.
3. Platforms in Focus: Proxmox VE, OpenStack, and KubeVirt
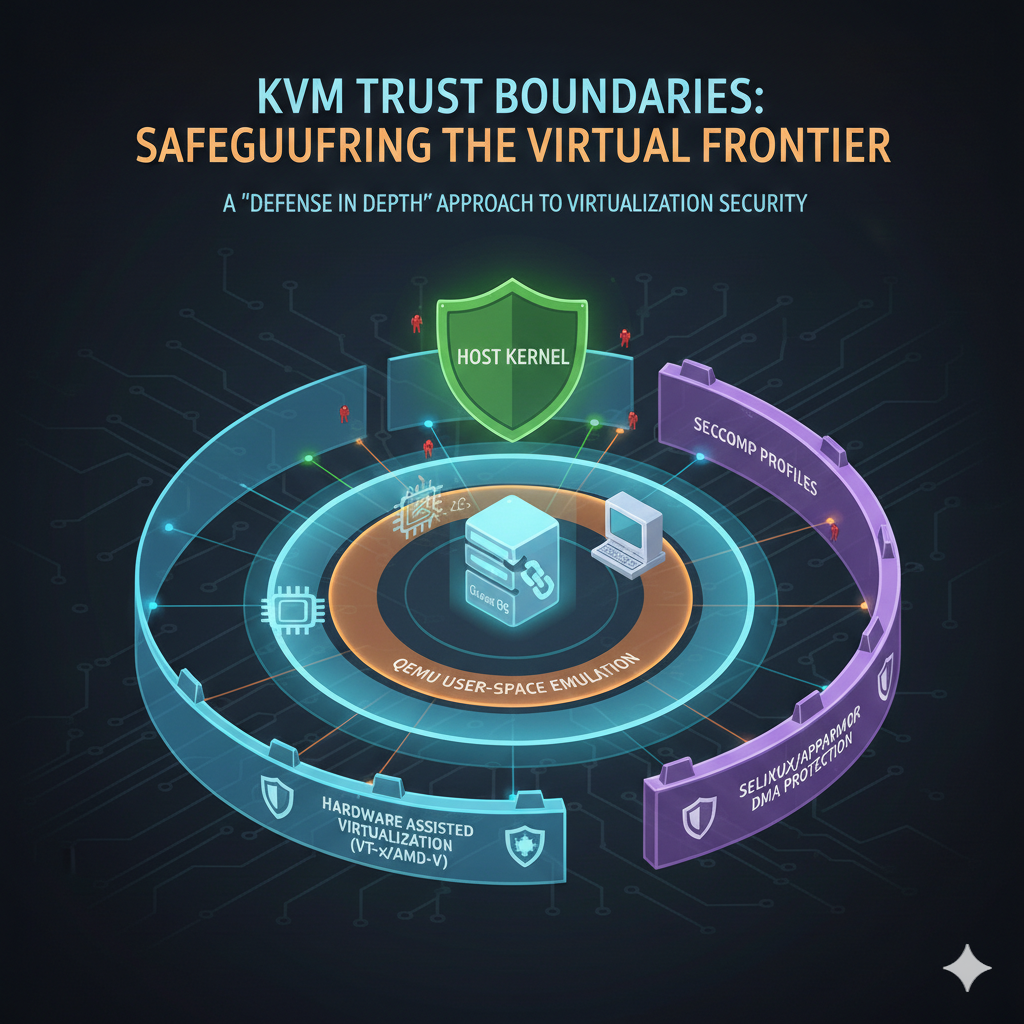
To achieve true digital sovereignty, the underlying software must be as transparent as the hardware it runs on. For the Linux admin, this means moving away from proprietary hypervisors and toward a stack built on KVM (Kernel-based Virtual Machine) and QEMU. While they share a foundation, the following three platforms offer different paths to autonomy.
Proxmox VE: The Pragmatic Sovereignty Entry point
Proxmox VE is often the first choice for organizations transitioning from VMware or legacy on-premise setups. It is “infrastructure-first” because it provides a bridge between traditional virtualization and modern containerization.
- The Sovereign Advantage: It uses a debian-based foundation with no hidden licensing “kill-switches.”
- Key Capability: Integrated support for ZFS and Ceph allows admins to build enterprise-grade storage clusters without buying expensive, vendor-locked SAN hardware.
- Ideal For: Small-to-medium government agencies or localized healthcare clusters that need high availability without the complexity of a massive cloud orchestrator.
OpenStack: The “Own-Your-Own-AWS” Powerhouse
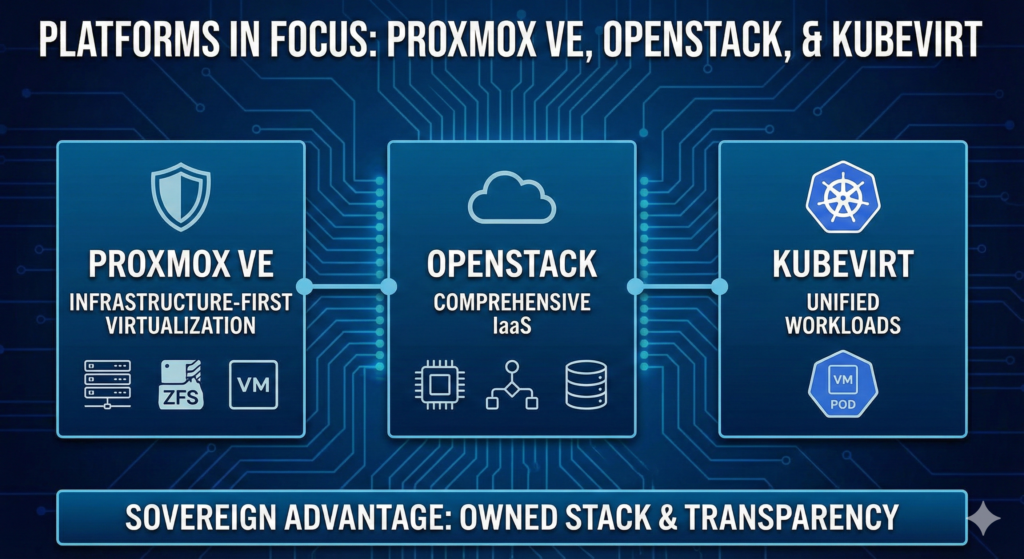
If the goal is to provide a true Private Cloud experience—complete with self-service portals, multi-tenancy, and complex networking—OpenStack is the industry standard.
- The Sovereign Advantage: It decouples the service from the provider. Because OpenStack is the backbone of many European sovereign clouds (like OVHcloud or T-Systems), an admin can move workloads between their own data center and a local provider with zero refactoring.
- Key Capability: Modular services like Nova (compute), Neutron (networking), and Cinder (block storage) allow for a highly customized “stack” that matches specific regulatory requirements.
- Ideal For: Large-scale deployments where “Infrastructure as Code” (Terraform/Ansible) is non-negotiable for compliance and auditing.
Comparison: Choosing Your Sovereign Foundation
| Feature | Proxmox VE | OpenStack | KubeVirt |
| Primary Focus | Ease of Use & Stability | Massive Scalability (IaaS) | Kubernetes Convergence |
| Complexity | Low to Medium | High | Medium (Requires K8s) |
| Multi-tenancy | Basic | Advanced | Via K8s Namespaces |
| Storage Paradigm | Local/Ceph | Highly Pluggable | Persistent Volumes (CSI) |
4. Proxmox VE: A Small Sovereign Cloud Example
Consider a regional government agency needing to retrieve PostgreSQL databases, file services, and legacy web applications from a hyperscaler due to data residency laws. With a small Linux team (3 admins) and limited infrastructure budget, they deploy a 3-node Proxmox VE cluster using mid-range Dell servers, use Ceph for distributed storage, and maintain VM-based workloads.
Deployment Details:
The team built their cluster on three Dell R640 servers with NVMe drives for Ceph OSDs. Migration from AWS involved converting EBS-backed instances using qemu-img, reconfiguring networking for on-premises infrastructure, and scripting the bulk of VM imports using Proxmox’s API.
Challenges Solved:
One legacy application required GPU passthrough for GIS rendering—something easily accomplished in Proxmox VE with PCI device assignment, but complex and expensive in cloud environments. The team configured passthrough in under an hour using standard KVM techniques.
Results:
This approach provides data locality, full visibility into every layer of the stack, and regulatory compliance—all managed with familiar Linux tools (SSH, Ansible, standard monitoring). The agency eliminated egress fees, reduced costs by 60%, and regained control over their infrastructure without sacrificing modern features like live migration, automated backups, and high availability clustering.
5. KubeVirt: Integrating VMs in Kubernetes
A financial services company sought a sovereign cloud solution with Kubernetes at the helm but faced a problem: not everything could be containerized immediately. Legacy Oracle databases, compliance-required Windows applications, and monolithic systems built over decades still needed traditional VMs.
Deployment Approach:
They deployed a bare-metal Kubernetes cluster across on-premises hardware, installed KubeVirt as a Kubernetes operator, and integrated Rook-Ceph for persistent storage. VMs run as Kubernetes custom resources, managed with kubectl alongside containerized workloads.
Why This Works:
KubeVirt allowed the team to manage VMs and containers through a unified control plane. Legacy databases continue running as VMs with dedicated CPU pinning and NUMA-aware placement, while new microservices deploy as containers. The same RBAC policies, GitOps workflows, and monitoring tools apply to both.
Migration Path:
As applications modernize, VMs gradually convert to containers—but there’s no forced timeline. A legacy payment processing system remains a VM, while the API layer serving it runs in pods. Network policies span both, and the operations team uses one set of tools for everything.
This approach achieves seamless operations, consistent policy application across all workloads, and a gradual modernization path without the pressure of “lift-and-shift everything to containers by Q2.”
6. Case Study: Swiss Healthcare Provider
A Swiss hospital network needed to comply with strict patient data protection laws while modernizing aging VMware infrastructure that was becoming prohibitively expensive. With 5 Linux admins and 150 VMs hosting electronic health records, imaging systems, and administrative applications, they evaluated both hyperscaler and sovereign cloud options.
The Decision:
After analyzing costs, compliance requirements, and operational complexity, they chose Proxmox VE over both AWS GovCloud and continuing with VMware. The key factors: full GDPR compliance without relying on vendor attestations, predictable costs, and maintaining patient data entirely within Swiss jurisdiction.

Deployment:
Five-node Proxmox cluster with Ceph storage, deployed on-premises across two data centers for disaster recovery. VMs migrated using automated scripts over a 12-week period, with Proxmox HA ensuring zero downtime for critical medical systems during the transition.
Outcome:
The hospital network achieved full data residency compliance, reduced infrastructure costs by 65% compared to AWS equivalents, and maintained complete control over patient data with no third-party vendor access. The team retained familiar Linux tools—SSH access, Ansible automation, Prometheus monitoring—while gaining modern features like live migration, incremental backups, and cluster-wide resource management.
Key Lesson:
Sovereign doesn’t mean sacrificing capabilities or accepting outdated technology. It means choosing where accountability lies and ensuring that sensitive data remains under your jurisdiction and your control.
7. The Road Ahead: Why Open-Source is the Only Path to True Sovereignty
The examples of the regional government and the Swiss hospital network illustrate a growing truth: Cloud is no longer a place you go; it is an operating model you adopt. When you “rent” a stack from a hyperscaler, you are beholden to their API updates, their pricing whims, and their jurisdictional vulnerabilities (such as the U.S. CLOUD Act). By contrast, building on an open-source foundation provides three distinct layers of protection:
- Auditability: You don’t have to “trust” a vendor’s compliance whitepaper. You can audit the code yourself or rely on a global community of security researchers.
- Portability: Because tools like KVM, QEMU, and Ceph are industry standards, you aren’t locked into a single hardware vendor or service provider.
- Skill Longevity: Training your team on standard Linux internals, Ansible, and Prometheus creates a “sovereign workforce”—talent that knows how infrastructure actually works, rather than just how to navigate a specific vendor’s dashboard.
Conclusion: Reclaiming the Stack
Digital sovereignty is often framed as a defensive move—a way to avoid fines or protect data. But as we’ve seen, it is also an offensive advantage. Organizations that own their stack are more agile, have more predictable costs, and can optimize their hardware for specific workloads (like GPU passthrough) without the “cloud tax.”
The Sovereign Cloud movement isn’t about being “anti-cloud”; it’s about being pro-control. By leveraging Proxmox VE, OpenStack, and KubeVirt, organizations are proving that you can have the convenience of modern cloud orchestration with the ironclad security of local ownership.
The choice is clear: You can either be a tenant in someone else’s digital kingdom, or you can build your own.